![]() Yesterday NXP released two new embedded ARM M-class controllers, the LPC18Sxx and LPC43Sxx, both with added AES. If that isn’t enough for you, there is also a companion security chip called A7, no relation to the homonym from ARM.
Yesterday NXP released two new embedded ARM M-class controllers, the LPC18Sxx and LPC43Sxx, both with added AES. If that isn’t enough for you, there is also a companion security chip called A7, no relation to the homonym from ARM.
It is hard to get overly excited about M3 and M4 cored devices but NXP has done something interesting with these two new parts, added a full 128-bit hardware AES engine. Know any uses for an embedded controller with high-end security? Things like cash registers, medical devices, utility meters, and all the rest come to mind rather quickly, all can use far more crypto throughput than the vanilla cores can manage in software. That said there are no calculations that the AES engine can that the cores can’t do as well, it is just a matter of how fast.
The LPC18Sxx is based on the ARM Cortex-M3 but the LPC1843Sxx has a twist, it has an M4F plus an M0. The M0 shares the bus and can take over low-level work for things like watchdogs or interrupt driven code that could cause a glitch in the main tasks. Adding an M0 core takes roughly zero space on a modern process but the bus and added logic for it likely takes up more area. There is irony to Moore’s law at times.
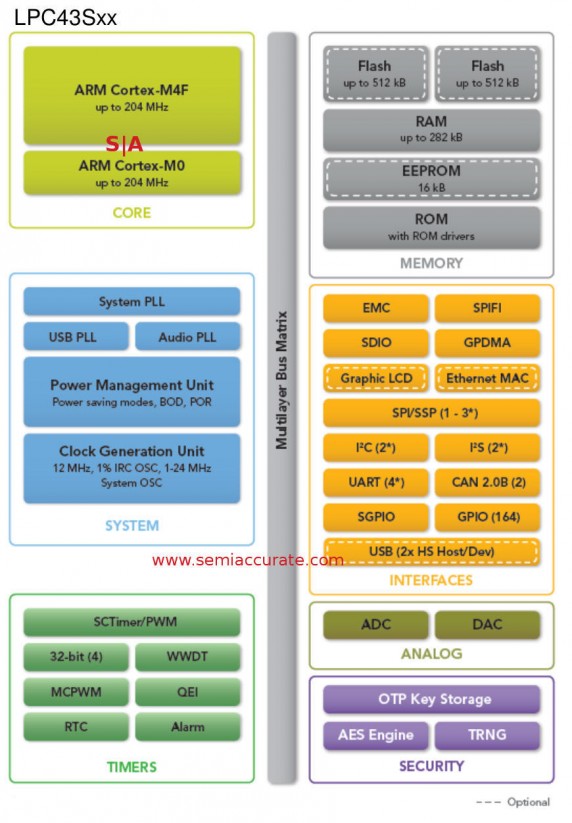
Options for the LPC43Sxx line
As you can see the systems aren’t all that complex but then again these are devices that start out in the $3 range for 10K units and go way way down if you have real volume. For that you get a solid microcontroller with USB, Ethernet, on-board flash, and the all important hardware crypto unit. These devices positively scream, “secure gateway”, don’t they?
Speaking of security, NXP claims that the new controllers have a true random number generator (RNG), unique keys per device via secure OTP key storage, secure boot, code protection, and of course the aforementioned AES-128 engine. About the only weak spot is software based connection authentication, at least for some definitions of weak.
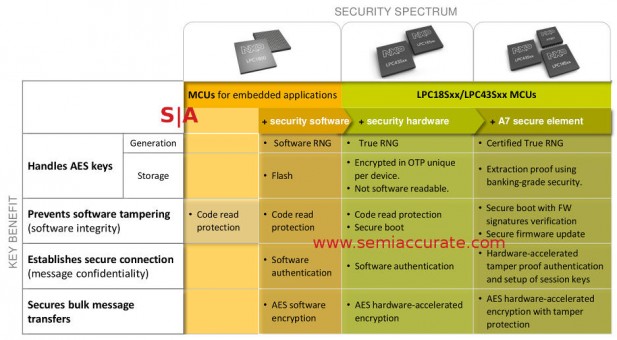
Secure, really secure, or borderline overboard?
If that isn’t good enough for you, you can add the A7, short for Authentication7 secure element co-processor. As you can see above, A7 has a certified RNG, insert NSA joke here, and the rest falls under two main headings. The first category is tamper proofing the parts, something that is technically impossible but quite effective when combined with per-device keys. If you can crack it, you will never recoup the costs. The other is that external connections are hardware based, handy if you are doing gateway type devices.
Update February 25, 2015 @ 10:45pm: We removed a sentence about the A7 costing only $.10 because it was wrong. NXP stated that the difference between AES bearing parts and non-AES versions was only about $.10 in large quantities, not that the number was the cost of the A7. We screwed up, sorry. We fixed it so we are less sorry now though.
What is more important than the specs and technical minutia is that this device line exists at all. By that we don’t mean a controller of this class with real security, those are all over the place already. The bit that got SemiAccurate’s attention was the fact that there is enough demand to push this kind of security into mainstream device hardware, not just a high-end specialized part. We think this will be a growing trend and one that will actually make a difference against some classes of attacks once they are ubiquitous. If everyone ends up jumping on this train, all the better.S|A
Charlie Demerjian
Latest posts by Charlie Demerjian (see all)
- What is Qualcomm’s Purwa/X Pro SoC? - Apr 19, 2024
- Intel Announces their NXE: 5000 High NA EUV Tool - Apr 18, 2024
- AMD outs MI300 plans… sort of - Apr 11, 2024
- Qualcomm is planning a lot of Nuvia/X-Elite announcements - Mar 25, 2024
- Why is there an Altera FPGA on QTS Birch Stream boards? - Mar 12, 2024